My favorite SSL provider (https://www.starfieldtech.com) recently increased their pricing from $7.99/year to $49.99/year. That felt like blatant abuse to me, so I’m canceling my services with them.
I’m now using the latest and greatest in SSL providers, Let’s Encrypt. It’s a well-support non-profit to provide CA (Certificates of Authority) for free. But, there’s a different kind of setup required to use it, so a little code is in order. I’ll document here how to use the system (including automatic renewals) when using Amazon Linux.
First, log in as the ec2-user, the standard way of logging into an Amazon Linux EC2 instance, then run the following commands:
sudo pip install -U certbot
# note, if pip is not available, you can download the certbot manually:
# wget https://dl.eff.org/certbot-auto
chmod a+x certbot-auto
If you’re using Amazon Linux 2, you’ll need to run somme additional commands, as documented by AWS:
cd /tmp
wget -O epel.rpm –nv https://dl.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpm
sudo yum install -y ./epel.rpm
sudo yum install python2-certbot-apache.noarch
In places where the text YOUR_WEBSITE_HERE appears, replace that text with your website domain. If additional websites are needed (such as a www version), append an additional “-d [extra_domain_here]” to the command below.
sudo ./certbot-auto --debug -v --server https://acme-v02.api.letsencrypt.org/directory certonly -d YOUR_WEBSITE_HERE
Note: If you need to protect multiple websites, append additional “-d YOUR_WEBSITE_HERE” arguments to the command above. Let’s Encrypt will generate a single set of keys that can be used to protect multiple websites.
Note: If using the Amazon Linux 2 instructions above, use an install command like this:
sudo certbot certonly --debug -v --webroot -d YOUR_WEBSITE_HERE
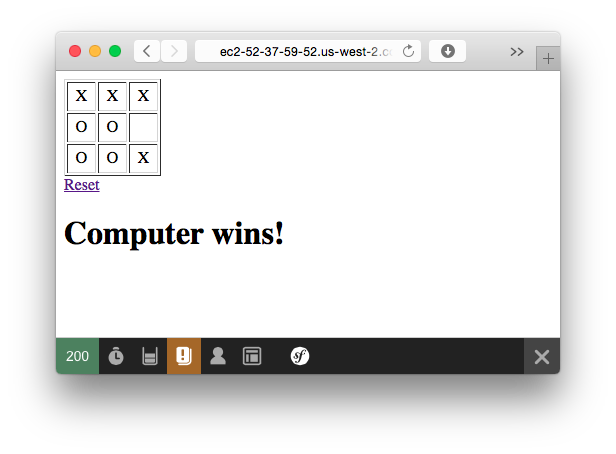
In the setup wizard you’ll come to a menu that looks like this:
How would you like to authenticate with the ACME CA?
-------------------------------------------------------------------------------
1: Apache Web Server plugin - Beta (apache)
2: Spin up a temporary webserver (standalone)
3: Place files in webroot directory (webroot)
-------------------------------------------------------------------------------
Select the appropriate number [1-3] then [enter] (press 'c' to cancel):
Chose option 3. I tried option 1, it didn’t work, and I didn’t want a temporary setup either. It’ll ask for an email address, legal agreement, opt-in to a newsletter, then another prompt:
Select the webroot for YOUR_WEBSITE_HERE:
-------------------------------------------------------------------------------
1: Enter a new webroot
-------------------------------------------------------------------------------
Press 1 [enter] to confirm the selection (press 'c' to cancel):
Since your only option is ‘1’, enter 1 and press enter.
Input the webroot for YOUR_WEBSITE_HERE: (Enter 'c' to cancel):
input /var/www/html and press enter
At this point the system will finish generating the certificates. You’ll now need to edit the apache config to tell apache to use these new certificates. Note: for this example, I’m assuming you’re running a web server with a single working directory and no virtual hosts.
sudo nano /etc/httpd/conf.d/ssl.conf
You’ll want to find the SSLCertificateFile, SSLCertificateKeyFile, and SSLCertificateChainFile entries and change their values to be as specified here:
SSLCertificateFile /etc/letsencrypt/live/YOUR_WEBSITE_HERE/fullchain.pem
SSLCertificateKeyFile /etc/letsencrypt/live/YOUR_WEBSITE_HERE/privkey.pem
SSLCertificateChainFile /etc/letsencrypt/live/YOUR_WEBSITE_HERE/fullchain.pem
Note: If encrypting multiple websites all at once, the “YOUR_WEBSITE_HERE” will be the first website name you used in the certbot-auto command above and that will be used for all websites you are encrypting.
Save your changes, then reboot the web server.
sudo service httpd restart
If the web server restarts successfully, you can try the https version of your site. It should be up and running at this point.
To set up a crontab that will automatically renew the certs as needed (since Let’s Encrypt only provides 90-day CAs), I like to use this code to get into a crontab manager:
sudo env EDITOR=nano crontab -e
Then add this line to have it automatically attempt to renew the certificate every day at 4:17AM UTC (a randomly selected time in the middle of the night):
17 4 * * * /home/ec2-user/certbot-auto renew --debug > /dev/null 2>&1
Save your crontab, and you’re good to go.
Much of this blog entry came from https://nouveauframework.org/blog/installing-letsencrypts-free-ssl-amazon-linux/
2017-12-14 Update: if you run into this kind of error, “Error: couldn’t get currently installed version for /opt/eff.org/certbot/venv/bin/letsencrypt”, run these commands (solution came from here):
rm -rf ~/.local/share/letsencrypt
sudo rm -rf ~/.local/share/letsencrypt
sudo rm -rf /opt/eff.org/certbot/
sudo /home/ec2-user/certbot-auto renew --debug